The Ultimate Cross-Platform Malware
The Mac Defender trojan scare confirmed what everyone has suspected all along: that Apple's products are vulnerable to malware after all!
But we can do better than that!
My new Computer Defender trojan, working on the same proven principles as Mac Defender, will eagerly attack a Mac, a PC, Commodore, Lisp Machine, UNIVAC, arithmometer, and just about any other computing device. The latter does not even need to be switched on or fully assembled! Behold:
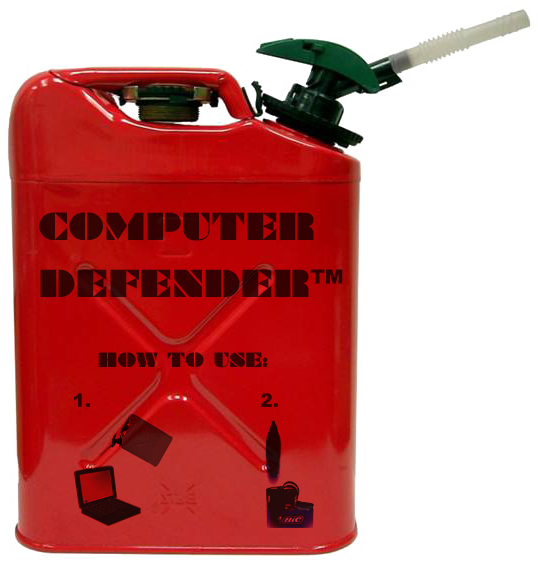
So, computer insecurity charlatans, how will you defend the public against this grave, unprecedented threat?



Those you call 'computer insecurity charlatans' will
put the OS on the network, so that your computational
state remains secure and accessible. That can be extended
with Tahoe-LAFS and like technologies to protect access
to private information from the hosting cloud.
Dear dmbarbour,
Well yes, time-sharing is back.
But there is no “Cloud”: There are only Other People’s Hard Drives.
And now you only need one tank of Computer Defender (and a set of lockpicks) - or a friendly politician - to hose everyone's data.
Or, an accident, or "an accident."
Google, "gmail locked out":
2,270,000 results.
Yours,
-Stanislav
There is no cloud. There is only water vapor in loose formation well above ground level.
What a silly, unproductive statement this would be!
Anyhow, any reasonable cloud storage will be both geospatially redundant and physically secure.
Among my own interest is in decentralized or 'network overlay' clouds, e.g. where different organizations and people are willing to auction some of their spare compute, storage, and bandwidth resources. Applications in such a cloud would position parts of the server near the client - and vice versa.
Dear dmbarbour,
If we lived in a world with
a) ubiquitous, ultra-low-latency Internet connectivity
b) ubiquitous, fully un-crippled public-key encryption
there would be no reason to prefer one's own, physically-owned CPU and storage resources to the "cloud."
But we do not live in such a world.
a) is technologically daunting but perhaps physically possible (at least when limited to a single planet.) b) is technologically simple but appears to be politically impossible.
I have no objections to the use of distributed computation and storage techniques for scientific computing. It is a perfectly reasonable thing to do.
On the other hand, those who push "the cloud" as a total replacement for the generic personal computer do not have users' best interests in mind.
The unspoken goals of the "cloud" advocates include fostering vendor lock-in, remote censorship, and, in the long-term: the expansion of the undetectable dragnet-style eavesdropping traditionally associated with telephony to personal computing.
Yours,
-Stanislav
I disagree with your simplistic characterization of 'cloud advocates'.
My own designs certainly oppose vendor lock-in - e.g. an overlay cloud could migrate work between vendors, based on rate competition and contracts they are willing to make for stability, intersected with the security policies of the users and developers.
The cloud (more precisely, lots of mini-clouds linked together to look like one big cloud) will replace the notion of personal computer. This is already happening. We transition to greater levels of mobile and wearable computing, ambient systems and augmented reality. In this world, users do not want their work tied to any particular device.
That said, using storage 'near' the user (including on the user's device) will always be part of the cloud model. Cloud doesn't just mean "other people's hard drives" - a device may be 'part of' an overlay cloud, rather than just a 'client of' it.
Public-key cryptography is certainly a useful building block. I don't see why you think it is 'politically impossible'. I haven't seen major issues with export regulations in many years. Tahoe-LAFS and E both make some use of public key encryption.
But any use of public keys that depends on a web-of-trust, such as certificate authority or PGP, certainly are broken. Seriously, there's a fundamental issue there: trust is not a binary condition; we trust different people with different things.
As long as we stick to the capitalism, you might as well just oppose basically everything.
Everything that arises, including cloud computing, will only further the cause of capitalist social domination. Smarter computing architectures will just serve to assist the imperialist military and other malevolent organisations.